Silent Order Post
Silent Order Post (SOP) is a service that offers the buyer more security and control over the checkout experience; it is ideal for stores that do not have the structure to comply with all PCI DSS security requirements for the use of credit cards.
Silent Order Post allows you to send your customer's payment data securely, directly to our system. The buyer's card data, such as card number and expiration date, do not travel through the store environment and are stored in encrypted form (token) in our environment, which is PCI DSS certified.
What is PCI DSS certification?It is a global standard for card data security. PCI DSS was developed to encourage and improve payment data security and facilitate the widespread adoption of consistent data security measures.
Certification is mandatory for an e-commerce company to receive, process and store card data.
Main benefits
- Direct data collection: payment data is collected directly from our systems by a script, through the fields defined in your checkout;
- Full compatibility: the solution is compatible with all payment methods available on the API Cielo E-commerce (national and international);
- PCI DSS certification: Our certification guarantees full compliance with card industry standards, reducing the scope of PCI DSS;
- Customized checkout: customization offers full control over the checkout experience and elements of your brand.
Supported payment methods
Silent Order Post is capable of encrypting credit, debit, voucher and multiple cards, as long as they comply with the mod10 format.
How it works
The store integrates the Silent Order Post script on the checkout page (client-side). When the buyer enters card details at checkout, this data is passed directly to our environment via the installed script. Our API generates a temporary token for the buyer's card, the PaymentToken, which must be used by the store to request authorization of the transaction. This way, sensitive card data does not pass through your e-commerce environment.
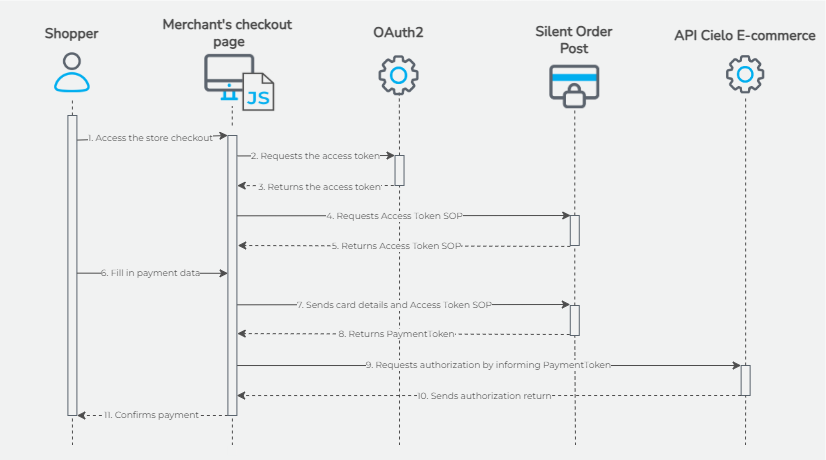
- The buyer accesses the store's checkout screen;
- The checkout page script requests the
access_tokenfor the OAuth2 authenticator; - OAuth2 returns the
access_token; - The checkout page script requests the
access_tokenfrom the Silent Order Post (access_tokenSOP), informing theaccess_tokenobtained in the previous step; - The Silent Order Post returns the
access_tokenSOP; - The shopper fills in the payment data on the checkout screen;
- The checkout page script sends the card data to the Silent Order Post, informing the AccessToken SOP;
- The Silent Order Post returns the
PaymentToken(encrypted card); - The checkout page script sends the
PaymentTokento the store's server, and the server sends the transaction authorization request to the API Cielo E-commerce, informing thePaymentToken; - The API Cielo E-commerce returns the authorization response;
- The store confirms the shopper order, if desired.
Silent Order Post allows for more security without interfering with your page layout.
Updated 6 months ago